The internet is a vast network of computers that are interconnected to share information. The term “internet” is used in two different ways: it can refer to the entire global system of interconnected computer networks, or it can refer more narrowly to just one type of network – the part that deals with non-voice data communication.

The Internet connects millions and billions of people all over the world who use it for many different purposes, from social media sites like Facebook and Twitter, online shopping sites like Amazon and eBay, email services such as Gmail and Yahoo Mail, video streaming websites like YouTube or Hulu Plus, cloud computing storage providers such as Dropbox or SugarSync … etc.
In this post, we will be exploring some common internet terms that you might not know, but would benefit to learn about. These are computer-related jargon which is used when communicating with other people interested in internet era.
Glossary of Internet Terms

A
- Avatar: An avatar is your virtual persona in the digital world, whether you’re gaming or participating in online communities. It’s the character or icon that stands in for you, letting you interact and express yourself in the cyber universe.
B
- Bandwidth: Think of it as the highway of the internet. More bandwidth means more lanes, so information can travel faster. It’s crucial for things like streaming your favorite shows without buffering.
- Blog: A blog is a website that is maintained by a person (or even a group of people) and made available for public viewing in an ongoing fashion. With the advancement of technology, it has become possible to update one’s blog from anywhere in the world via email or your smartphone, tablet…etc
- Bot: A bot is a piece of software designed to mimic human interaction, especially in chat environments, or to automate repetitive jobs. It’s like having a digital assistant that can chat with you, answer questions, or carry out tasks without needing a coffee break.
C
- Captcha: A quick test to prove you’re human. You’ve probably encountered those quirky images and letter combinations.
- Cloud Computing: Cloud computing is the internetworking of computer networks whereby shared resources, software and information are provided to computers and other devices on demand, like the websites you visit that offer free storage space in exchange for signing up or similar services.
- Cookie: Not the delicious treat, but almost as popular! Cookies are small files stored on your computer by websites. They remember your preferences, making your online experience smooth and personalized.
- Cyberbullying: Cyberbullying is the act of harassing or intimidating someone over the internet, using platforms like social media, chat rooms, or email. It’s basically being mean or abusive to someone online, and it’s a definite no-go in any digital community.
D
- Domain: A domain is the web address that you type into your browser to visit a website. Think of it as the online “street address” that helps you find where a site lives on the internet.
E
- E-Commerce: This refers to the electronic transfer of funds or digital information between two parties in order to settle a financial transaction online.
- Email: Email is a form of electronic messaging between two people or groups in which text, images…etc are sent via an interconnected system of computers over the internet. Emails typically appear in the recipient’s inbox when they are online if their email client is turned on and configured to do so at that time. Most news websites include “email this story” links under every entry, allowing visitors to easily send stories to anyone else with an email address by simply clicking a link contained within any article.
- Email Spam & Filters: One method used by email service providers (such as Gmail and Yahoo Mail) to fight spam emails (unsolicited emails) is to apply a set of rules on incoming mail and weed out those that meet specific criteria. The email’s sender and content are analyzed, and if the receiver decides that certain criteria (such as whether it comes from an unknown person or sender) matches some configured values, the message is considered spam and automatically moved to a separate folder/label for further review. Most email service providers allow users to configure these parameters as they wish in order to provide the best experience for their own personal use.
- Encryption: Encryption is the process of encoding messages or information in such a way that eavesdroppers or hackers cannot read it but that authorized parties can. There are several encryption algorithms used today by many people, but the most common are RSA, AES and ECC.
F
- Firewall: A firewall is a networking device that controls traffic between two networks by analyzing incoming network packets. If it finds an unauthorized packet, it will drop it before reaching its destination.
H
- Hashtag: The #hashtag is the social media superstar! It helps you connect with others, follow trends, or express your feelings. Put it before any word or phrase, and you’ve got an instant conversation starter!
- HTTP: Hypertext Transfer Protocol (HTTP) is an application protocol for distributed, collaborative, hypermedia information systems. In simple terms it’s just a way that computers communicate with each other over the internet – allowing them to send requests and receive responses. HTTP is the basic protocol of the web, along with which come other standards like HTML (and XML), URLs…etc.
- HTTPS: Hypertext Transfer Protocol Secure (HTTPS) is an extension of HTTP for secure communication over a computer network. Network computers use HTTPS when transmitting sensitive information such as credit card numbers, social security numbers or bank account information.
- HTML: HTML stands for “HyperText Markup Language” and it is used to create hypertext documents that are suitable for publishing on the World Wide Web (WWW). The term “web page” is sometimes used interchangeably with “website” but in reality it can be any document within a website or even multiple websites. The document is then “tagged” with HTML commands that describe its appearance (such as font, color and alignment) and its function (such as headers, links…etc).
I
- IoT: Imagine your fridge telling your phone you’re out of milk. That’s IoT! It’s all about connecting everyday devices to the internet, allowing them to collect and exchange data. Cool, huh?
- IP Address: An Internet Protocol (IP) address is a numerical label assigned to each device connected to a computer network that uses the Internet Protocol for communication. It’s basically a series of 4 numbers separated by periods that identifies your computer on the internet. The IP Address can be used in conjunction with domain name servers (DNS) to fully locate your machine over the web.
- ISP: This stands for “Internet Service Provider” which is an organization that provides services for accessing, using, or participating in the internet service.
M
- Malware: Malware refers to any set of programs designed to allow cybercriminals access to your system with or without your consent. Malware can be classified into many different categories, but they usually include viruses, worms, Trojan horses…etc.
- Meme: Ever seen a funny picture with a clever caption online? That’s a meme! These viral sensations can spread like wildfire, offering a good laugh or a thought-provoking message.
P
- Phishing: Phishing is a form of internet fraud typically carried out by sending out emails purporting to be from reputable companies with the goal of obtaining personal information such as credit card numbers…etc from unwitting victims. These emails usually direct the user to enter details at a fake website that then collects this information for illegal use.
- Proxy: Proxy servers act as middlemen between “clients” and the Internet. By connecting through a proxy, you can make it much more difficult for people to spy on your web-browsing habits or gather private information like your IP address…etc . A famous example of this is Tor (The Onion Router).
R
- Router: A router is a networking hardware device that forwards data packets between computer networks. Its algorithm determines its decision and routes the traffic based on a pre-defined rule set.
S
- SEO: Want your website to shine in search engine results? SEO is your best friend! It’s all about making your site more attractive to search engines like Google by using relevant keywords, snappy titles, and quality content.
- Social Media: Social media refers to websites such as Twitter, Facebook, Instagram…etc which serve not only as means of communication but also outlets through which people can share their views with the entire world – thus allowing and individuals alike have a major online presence or “social media profile”.
- Spam: Spam is the digital equivalent of junk mail, flooding your inbox with unsolicited emails usually pushing products or services you didn’t sign up to hear about. Think of it as the annoying clutter that you have to sift through to get to your actual, important emails.
T
- Trojan Horse: The term Trojan Horse is derived from Homer’s Iliad, where the Greeks used a large wooden horse to sneak their warriors into Troy. Similarly, a Trojan Horse is a set of codes in an application that allows attackers to remotely access and control your computer system. Sometimes, malware can be disguised as a video codec or flash player update which users are prompted to download when they visit especially malicious websites.
U
- URL: A Uniform Resource Locator (URL) specifies the location of something on the Internet. They are used to identify everything from websites to e-mail addresses.
V
- VPN: Short for “Virtual Private Network”, this allows users to securely access other private networks across shared or public networks while maintaining privacy through security procedures and tunneling protocols.
X
- XML: XML stands for “Extensible Markup Language” which was designed to allow developers to design their own customized markup languages without having to develop the entire language from scratch.
W
- Website: A website is a collection of related web pages containing text, images, videos or other digital assets. The initial connection between one browser and one server is called a request. That request may have been initiated by the user clicking an item in a list, typing a URL directly into their browser, or entering a search term in a search engine’s webpage.
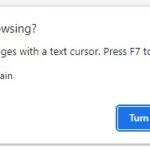
- Web Browser: A web browser is a software application designed to allow you access to websites on the internet. It can include features such as page zooming…etc . Some examples are Safari, Chrome, Edge, Internet Explorer… etc
- Webinar: A webinar is essentially a seminar that’s hosted online, offering a convenient way to engage in learning or share expertise without leaving your house. Think of it as a virtual classroom or conference room where presentations, workshops, or discussions can take place.
- Wi-Fi: Wi-Fi is your wireless ticket to the internet, letting your devices like smartphones, tablets, and laptops connect without any cables. It’s like the invisible bridge that links your gadgets to the web, allowing you to browse, stream, and work on the go.