A WPA key is a wireless network security protocol designed to protect your wireless signal against unauthorized access. It uses a key that changes automatically at regular intervals, which can be up to every 100 seconds. For this reason, it’s considered one of the best methods for keeping your wireless signal secure!
What is a WPA key?
I’m going to show you what WPA keys are and how they’re used in just two minutes – don’t worry, I’ll keep it short and sweet!
The first thing you need to know is that there are two types of WPA keys – personal and enterprise. A personal WPA key can be up to 63 ASCII characters in length, while an enterprise WPA key can be much longer!
A personal WPA Key is used in home networks, where the owner knows the password so there’s no need for another person to access it.
An enterprise WPA key is used in businesses, universities, and schools. To gain access to the network you’ll need a username and password in addition to your regular wireless security protocol. Since employees may change jobs or leave the company, this ensures that visitors or guests will not be able to use or gain access to your wireless if they’re no longer employed by the company.
There! Now you know what a WPA key is and how they’re used to keep your wireless secure! I’m sure you’ll find this useful in the future if anyone ever asks, “What is a WPA key?” Which was the question we started with, so there’s no going wrong here!
Where can I find my WPA key?
The key can be requested from the person who manages the network, even if you’re using a public Wi-Fi hot spot or one at a business site. If you’re staying at someone’s home, try asking for the network password.
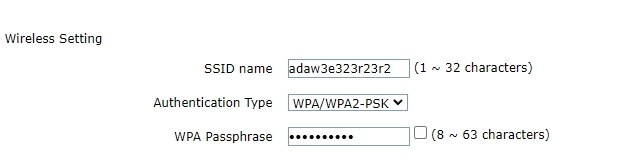
If you’re not sure what your wireless router’s password is, check on it. A common default password or passphrase will be printed on the device and labeled “WPA Password” or “Network Security Key,” as a result of which you can access it.
On your router, you’ll often see an SSID number. This is the default name for your network. You can usually access your router’s configuration.