A hash key, also sometimes called a hash code or just a hash, is a unique identifier for data. Hash keys are used in various settings such as cryptography and computer programming. In simpler terms, a hash key is just a number that corresponds to some piece of data. When you want to retrieve that data, you can use the hash key to look it up.
Hash keys are typically generated by a mathematical algorithm, which means that they are usually long and difficult to guess. This makes them ideal for use in security applications, where you want to make sure that only authorized users can access the data. Hash keys can also be used to verify the integrity of data since any change to the data will result in a different hash key.
If you’re a gamer, you’ve probably heard of SteamID64. These are hash keys that are used to identify players on the Steam gaming platform. If you want to add someone as a friend on Steam, you’ll need their SteamID64. You can find your own SteamID64 by logging into your account and going to your profile page.
Hash keys can be generated for any kind of data, but they are most commonly used with digital data. This is because it is easy to generate a hash key for a piece of digital data, and it is also easy to verify the integrity of that data using the hash key.
Hash Key in a Hash System
A hash system work by taking bigger data and converting it to smaller, fixed-length hash key. The original data can later be retrieved by using the key. Hash keys are used in such systems as passwords and lock combinations.
The benefits of using the hash key in these systems are efficiency and speed. It’s much easier to remember a word or phrase as a hash key, and hashes shorten the amount of time it takes for the system to process information.
In addition to using the hash key as a shortened version of big data length, they’re also used by people on social media sites like Twitter or blogging sites like Tumblr. Hash keys are used on these sites to categorize posts so that people can more easily find the post they’re looking for.
For example, if someone has a Tumblr blog with multiple posts, using hash keys allows them to label their posts for easier retrieval. A hash key might be the name of the category or topic that the post falls under.
Hash Key in Password Protection
Hash keys are also used for security purposes to encrypt passwords. For example, if you have an online account where all your personal information is stored, then you might use a password to access that account.
If your password gets hacked into by someone else who tries to log into your account without permission, then one-way security experts recommend protecting yourself is by using a very long string of letters and numbers as your password instead of just something like “password123” which would make it easier for hackers to figure out what you used.
If your password is very lengthy, then even if the hacker gets into your account it will take them longer to figure out what your real password was.
While password security is good for protecting yourself from hackers, sometimes you might not want others to know what your passwords are because they can’t access your online accounts without knowing the correct one, so this is where hash keys have come in handy.
Instead of using your actual password as a key to open up an account on whatever site you are using, now hash keys are used to encrypt passwords so that nobody can tell what it really is unless they’re trying to hack into an account and only find out which one it actually is after going through every possible one.
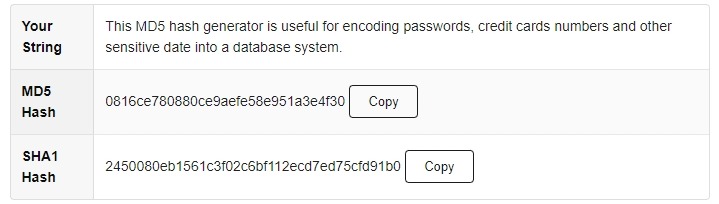
The way that hash keys are used to encrypt passwords is by taking the password that you want to use, and then using another program like MD5 (Message-Digest algorithm 5) to convert it into a string of seemingly random letters and numbers with no discernible pattern or meaning in order to keep this information secure so nobody can figure out what your real password was.
However, even though hackers would have to go through every possible combination with all these hashes before they find the one correct string that has the right number of characters for whatever site you’re trying to sign up for, if they know what hashing function was used on your account then it might be easier than having to test every single possible letter and number sequence.
For example, if someone wanted to hack into your account on a site called “SuperTechSite” and they knew that you used MD5 hashes on your password, then an algorithm like this is usually more secure because there are multiple numbers involved in creating one hash key.
This means that even if the hacker knows what hashing function you used it still might be somewhat difficult for them to figure out what your password really was as opposed to sites that only use single-number hashing functions where if the hacker knows how the hashing function works then they can easily crack your password without having to go through all possible combinations of letters and numbers until they figure it out.
In order to make sure that you have a super-secure password but also so that you can remember what it actually is, try using a string of random words instead of just using some letter and number sequence.
This way even if somebody was trying to figure out what your password as they would have to guess which word in the series of words might be your actual password without getting it right on their first try.