In today’s digital world, the need for computer security has become more significant than ever. Computer security refers to the protection of computer systems and networks from unauthorized access, theft, or damage. The primary objective of computer security is to ensure the confidentiality, integrity, and availability of computer systems and data. In this article, we will discuss the different types of computer security.
What is Computer Security?
Computer security is a crucial aspect of cyber security that involves protecting computer systems, networks, and data from unauthorized access, theft, damage, or disruption. It encompasses a range of technologies, processes, and practices that are designed to safeguard computer systems and data from various threats, including malware, viruses, hackers, and other cyber criminals.
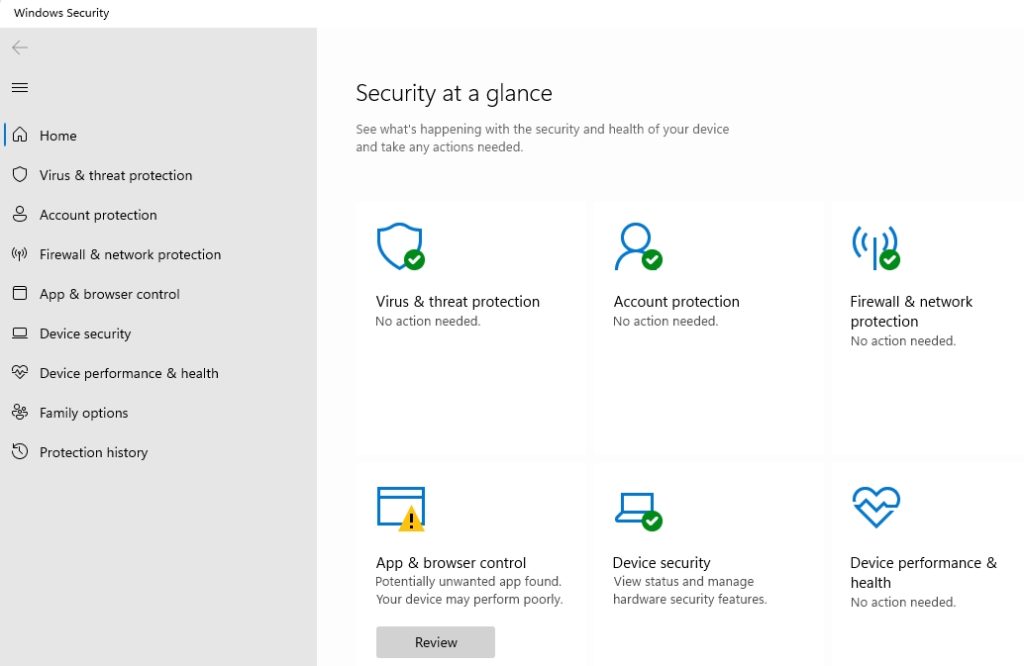
Effective computer security involves implementing various security measures such as firewalls, antivirus software, intrusion detection and prevention systems, access controls, encryption, and backup and recovery systems. These measures are designed to prevent unauthorized access to computer systems and data, detect and respond to security breaches, and ensure the confidentiality, integrity, and availability of critical data and systems.
Computer security is an ongoing process that requires continuous monitoring, testing, and updating to ensure that systems and data remain secure against evolving threats and vulnerabilities.
Types of Computer Security
Network Security
Network security is a type of computer security that involves securing a computer network from unauthorized access, misuse, modification, or denial of service attacks. The main goal of network security is to protect the network and its resources from malicious attacks. Network security can be enhanced by implementing various techniques such as firewalls, intrusion detection systems, and encryption.
Firewalls are used to block unauthorized access to a network by analyzing incoming and outgoing traffic. Intrusion detection systems monitor network traffic for signs of unauthorized access or malicious activity. Encryption is used to protect sensitive data by converting it into an unreadable format that can only be decrypted with a secret key.
Data Security
Data security refers to the protection of data from unauthorized access, disclosure, or modification. Data is a valuable asset for any organization, and its security is crucial to maintain the confidentiality and integrity of the data. Data security can be enhanced by implementing various methods such as access control, encryption, and backups.
Access control is used to restrict access to data based on the user’s role or privileges. Encryption is used to protect sensitive data by converting it into an unreadable format that can only be decrypted with a secret key. Backups are used to make copies of data to ensure that it is not lost due to hardware failure or other issues.
Application Security
Application security is a type of computer security that involves securing software applications from cyber attacks. Applications are susceptible to various types of cyber-attacks such as SQL injection, denial of service (DoS) attacks, and data breaches. The main goal of application security is to ensure that applications are designed and developed with security in mind. This involves adding security features within applications to prevent cyber attacks and protect the application’s users and data.
Application security can be enhanced by implementing various techniques such as secure coding practices, penetration testing, and code analysis. Secure coding practices involve developing software applications with security in mind. Penetration testing involves simulating a cyber-attack to identify vulnerabilities in the application. Code analysis involves analyzing the application’s code to identify any security issues that may exist.
Internet Security
Internet security is one of the most critical aspects of modern-day digital life. With the advent of the internet and the creation of online networks, the scope of potential security breaches has increased exponentially.
Internet security is all about protecting your computer and online activities from harmful attacks. These attacks can come in many forms, such as hacking, computer viruses, malware, and denial of service attacks. From personal identity theft to hacking into sensitive corporate information, cyber-criminals have become increasingly adept at infiltrating even the most secure online systems.
One of the key components of internet security is ensuring that sensitive data remains encrypted at all times. Encryptions ensure that sensitive information remains protected from outside attacks or data breaches. Additionally, internet security protocols ensure that users remain protected from malicious software, viruses, and phishing attacks.
This includes ensuring that systems are regularly updated with the latest security patches and feature advanced security measures such as firewalls and intrusion detection systems to prevent unauthorized access to sensitive data.
By staying vigilant and using the latest in security technology, individuals and businesses can better protect themselves from the numerous risks associated with operating in the digital world.
Internet security recommends robust password management. One of the main problems with password security is that users tend to employ the same password across different accounts, even if they are associated with different levels of sensitivity. This makes it significantly easier for hackers to gain access to sensitive information, as they have only to obtain one password to access multiple accounts.
As such, password managers have become increasingly popular as they allow users to use strong, unique passwords for each account, which are near-impossible to crack.
Strong passwords in conjunction with advanced security protocols help to create a safe digital environment, which ensures the privacy and security of individuals and businesses online.
Endpoint Security
Endpoint security refers to the protection of computer systems from cyber attacks through human error. The biggest security risk in any organization comes from its end users who may lack awareness and knowledge about cyber security policies and procedures. This can inadvertently open doors for cyber attackers. To prevent this, organizations need to ensure that their users understand comprehensive security policies and procedures.
It is important to provide security awareness training to users, covering topics such as cyber security, phishing and social engineering attacks, password creation and usage, device security, and physical security. This will help users to understand the importance of cyber security and take necessary precautions to protect sensitive information.